Insurance verification is a key process for healthcare practices, which has a significant impact on revenue as well as patient satisfaction. It has to be accurately completed even before the patient visits the provider, to confirm the patient’s eligibility and benefits. With the healthcare industry increasingly relying on digital processes, ensuring the confidentiality, integrity, and availability of patient information during verification of patient benefits process becomes paramount. Technology integrated insurance verification enhances efficiency while maintaining the highest standards of data security. Security is a major consideration when performing verification and, in this post, we examine some best practices for securing healthcare data in eligibility checks.

OSI can verify coverage for all insurances including federal and commercial plans.
Learn more about our insurance verification services.
SPEAK TO AN EXPERT TODAY!
Safeguarding Patient Data during Insurance Eligibility Verification
It is important to adopt a layered security model that includes the implementation of intrusion detection systems, firewalls, and consistent monitoring to spot and address threats in real time.
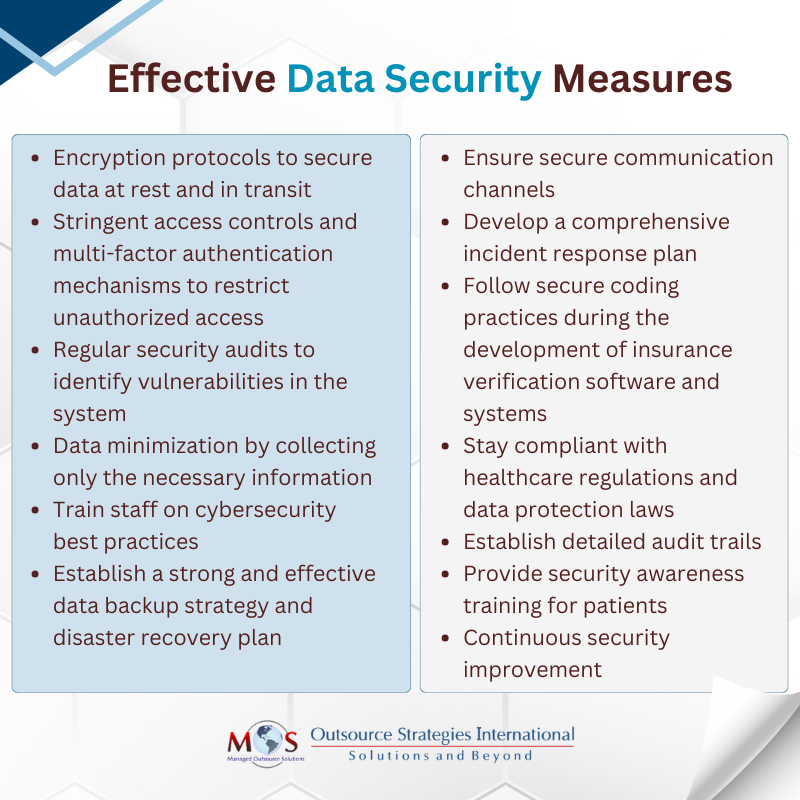
Encryption Protocols: Implement robust encryption protocols to safeguard data both in transit and at rest. Utilizing strong encryption algorithms ensures that sensitive information remains confidential during communication between various systems. Encryption protocols include AES (Advanced Encryption Standard) which is known for its robustness, and TLS (Transport Layer Security) that is used to secure data in transit over networks. Another method is full-disk encryption on storage devices, this ensures that the data remains inaccessible even if the storage device is compromised.
Access Controls and Authentication: Establish stringent access controls and multi-factor authentication mechanisms to restrict unauthorized access. This helps in preventing unauthorized personnel from accessing patient data and ensures that only authorized individuals can perform insurance eligibility checks.
Regular Security Audits and Monitoring: Conduct regular security audits to identify vulnerabilities in the system. Continuous monitoring is vital to detect any suspicious activities promptly, enabling proactive responses to potential security threats.
Data Minimization: Adhere to the principle of data minimization, collecting only the necessary information required for insurance eligibility checks. Reducing the amount of stored data minimizes the risk in case of a security breach.
Employee Training and Awareness: Train staff on cybersecurity best practices and raise awareness about potential threats. Employees should be well-versed in recognizing and reporting suspicious activities to minimize the risk of insider threats.
Data Backups and Disaster Recovery: Establish a strong and effective data backup strategy and disaster recovery plan to ensure quick restoration of data in case of system failures, natural disasters, or cyberattacks. Regularly test these procedures to ensure their effectiveness.
Secure Communication Channels: Make sure that the communication channels used for insurance eligibility checks are secure. Employ virtual private networks (VPNs) and secure connections to protect the data transmitted between different systems and entities.
Incident Response Plan: Develop a comprehensive incident response plan outlining the steps to be taken in the event of a security breach. This plan should include communication protocols, escalation procedures, and actions to contain and remediate the breach.
Secure Development Practices: Apply secure coding practices during the development of software and systems used in patient eligibility verification. Regularly update and patch software to address vulnerabilities and ensure the overall security of the system.
Regulatory Compliance: Stay compliant with healthcare regulations and data protection laws, such as the Health Insurance Portability and Accountability Act (HIPAA) in the United States. Compliance helps in maintaining the privacy and security of patient information and avoids legal consequences.
Audit Trail Implementation: Establish detailed audit trails that log all access and modifications made to patient data during insurance eligibility checks. Audit logs help in forensic analysis and tracking any unauthorized activities.
Security Awareness Training for Patients: Educate patients about the importance of cybersecurity and their role in protecting their own health data. Encourage them to use secure portals for communication and provide guidelines on identifying potential scams.
Continuous Security Improvement: Implement a continuous improvement cycle for security measures. Regularly reassess and update security protocols to adapt to evolving cybersecurity threats and technological advancements.
Cybersecurity Concerns in Insurance Eligibility Verification
Phishing Attacks: Guard against phishing attacks that target employees responsible for patient eligibility verification. Training staff to recognize and avoid phishing attempts helps prevent unauthorized access to sensitive data.
Ransomware Threats: Implement robust backup systems to mitigate the impact of ransomware attacks. Regularly updating and testing backups ensures the ability to recover critical data in case of a security incident.
Third-party Security: Assess and monitor the security practices of third-party vendors involved in the insurance verification process. Ensure that they adhere to stringent security standards to prevent vulnerabilities in the overall system.

Data Security Software – Types & Examples
- Firewall solutions: Cisco Firepower is a strong tool that helps control and monitor incoming and outgoing network traffic. The firewall acts as a barrier between the internal network and unreliable external networks, preventing any unauthorized access.
- Endpoint protection: This software provides a layer of defense for individual devices, protecting against ransomware, malware and other threats that target endpoints such as computers and mobile devices. An example of this type of software is Symantec Endpoint Protection.
- Encryption Software: Robust software such as McAfee Complete Data Protection ensures that the sensitive healthcare data is secure, whether at rest or in transit. Encryption solutions help you comply with data protection regulations and prevent any kind of unauthorized access.
- Security Information and Event Management (SIEM): These tools enable real-time analysis of security alerts generated in your organization’s technology infrastructure. An example is Splunk Enterprise Security software.
- Identity and Access Management (IAM): This type of software, for instance, Okta, helps manage user identities and control access to systems. Security is enhanced with multi-factor authentication, access controls, and single sign-on.
- DLP or Data Loss Prevention: A good example of a DLP tool is Digital Guardian, which monitors and controls sensitive data to prevent unauthorized access, sharing or leakage.
- Intrusion Detection and Prevention Systems (IDPS): IDPS softwares, like Snort, monitor network and/or system activities for malicious activities or security policy violations. They can automatically respond to or block such activities, enhancing overall security.
- Secure Email Gateways: Proofpoint Email Protection is one example of this type of software that helps prevent phishing attacks, malware, and other email-borne threats. They filter and scan incoming emails for potential security risks.
- Vulnerability Management: Vulnerability management solutions, like Tenable.io, scan and identify weaknesses in systems and applications. Regular assessments and patch management help mitigate vulnerabilities and enhance overall system security.
- Mobile Device Management (MDM): MDM solutions, such as VMware Workspace ONE, assist in securing mobile devices used by healthcare professionals. They enable organizations to enforce security policies, monitor device compliance, and remotely manage devices.
Protecting patient information during insurance eligibility checks is essential though resource-intensive. By incorporating reliable software solutions into their cybersecurity strategy, healthcare practices and health insurers can strengthen their defenses and better protect patient information during insurance eligibility checks. It’s critical to regularly update and adapt these tools to address evolving cybersecurity threats.